24/7 Phone Support
(231) 591-4822
Toll Free: (877) 779-4822
Walk-up Support
8 a.m. - 4:30 p.m.
UCB 108
IT Core Service Support
8 a.m. - 5 p.m.
What is the value of hacked email, website account, or computer?
“Hacked” in the context of this announcement is defined as stolen, compromised, or otherwise accessed account/computing asset without the authorization and often knowledge of their owner. The attackers can hack into an account to gain system access or they can gain system access and then harvest accounts that reside on the computer stored in browsers, the computer memory, or computer files (plain text and even password protected files with easy to guess password).
Picture is worth a thousand words:
Figure 1. Value and uses of hacked email.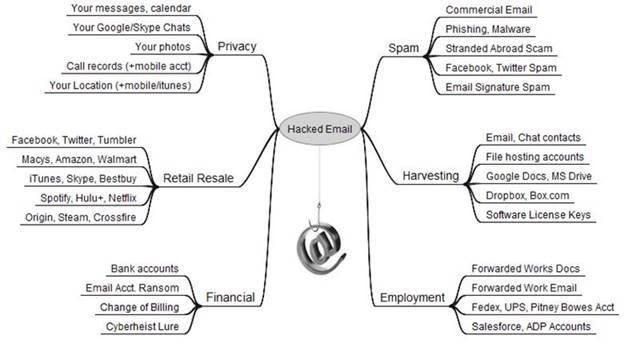 Source: https://krebsonsecurity.com/2013/06/the-value-of-a-hacked-email-account/
Source: https://krebsonsecurity.com/2013/06/the-value-of-a-hacked-email-account/
Figure 2. Value and uses of of Hacked PC.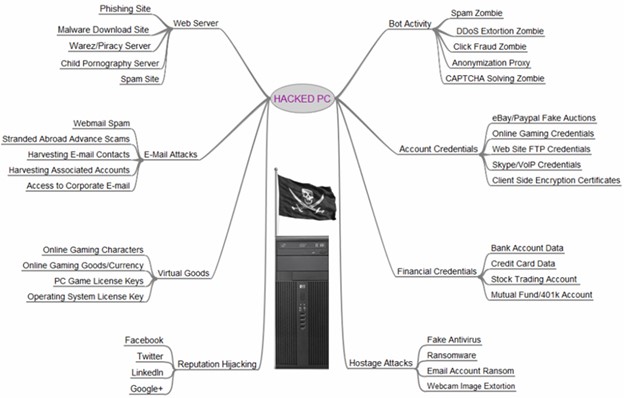 Source: https://krebsonsecurity.com/2012/10/the-scrap-value-of-a-hacked-pc-revisited/
Source: https://krebsonsecurity.com/2012/10/the-scrap-value-of-a-hacked-pc-revisited/
Figure 3. Stolen account economics.
Source: https://krebsonsecurity.com/2017/12/the-market-for-stolen-account-credentials/
What is the impact on the University of a compromised account or computer?
What can we do?
Do not use @ferris.edu account for personal business. When we detect that your @ferris.edu is part of reported cyber security incident, we will do our best to notify you and take appropriate actions to minimize impact on the University.
Figure 4. Number of @ferris.edu accounts that ITS detected and assisted with in 2017.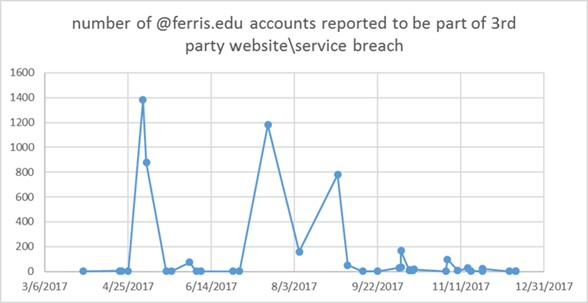
KnowBe4 Security Awareness Training (available for Ferris State University employees. After clicking the link, enter your email address in the web form. For example, [email protected])